cloud computing in cryptography
There is an increasingly prominent trend in many organizations to move a substantial portion of or even all information technology (IT) operations to an Internet-connected infrastructure known as enterprise cloud computing. As we know, with every technology there are security considerations.
For this discussion, please provide a thorough response to the below questions.
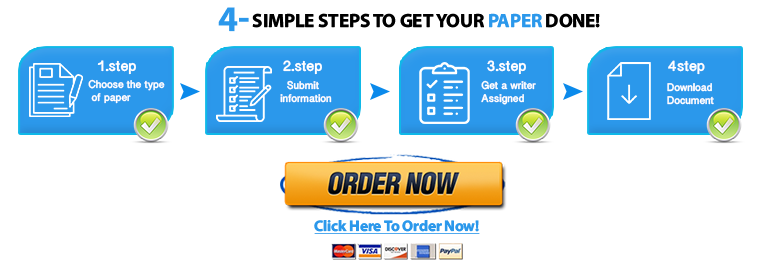
Save your time - order a paper!
Get your paper written from scratch within the tight deadline. Our service is a reliable solution to all your troubles. Place an order on any task and we will take care of it. You won’t have to worry about the quality and deadlines
Order Paper Now- Define cloud computing.
- List and briefly define three cloud service models.
- What is the cloud computing reference architecture?
- Describe some of the main cloud-specific security threats.
References for class
Required Reading
- Chapter 15: User Authentication
- Chapter 16: Network Access Control and Cloud Security
- Chapter 17: Transport-Level Security
Additional Resources
- https://www.professormesser.com/security-plus/sy0-501/pki-components/
- https://www.professormesser.com/network-plus/n10-006/user-authentication-2/
- https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-145.pdf
- https://www.professormesser.com/security-plus/sy0-401/cloud-computing-2/
Required Text
Required Text
Stallings, Williams. Cryptography and Network Security. Pearson, 2017.
Print ISBN: 9780134444284, 0134444280
eText ISBN: 9780134444635, 0134444639
"Looking for a Similar Assignment? Order now and Get 10% Discount! Use Code "Newclient"